Introduction to Linux and Cybersecurity
Introduction to Linux and Cybersecurity
1. What is Linux?
Linux is an open-source operating system based on the Unix architecture. It is widely used for servers, security testing, cloud infrastructure, networking devices, and cybersecurity operations.
The Linux operating system was originally developed by Linus Torvalds in 1991 and has since grown into one of the most important operating systems in the world.
Unlike proprietary systems such as Microsoft Windows or macOS, Linux allows users to view, modify, and distribute its source code freely.
Key Features of Linux
- Open-source and customizable
- Highly secure and stable
- Efficient resource management
- Strong networking capabilities
- Powerful command-line interface
- Multi-user and multitasking support
Linux powers many critical systems including:
- Web servers
- Supercomputers
- Cloud platforms
- Cybersecurity tools
- Network infrastructure
2. Importance of Linux in Cybersecurity
Linux plays a central role in cybersecurity because most security tools and testing platforms are built for Linux environments.
Many security professionals prefer Linux because it offers greater control, flexibility, and transparency compared to other operating systems.
Reasons Linux is Important in Cybersecurity
1. Security and Stability
- Linux has strong permission systems.
- Fewer vulnerabilities compared to many desktop systems.
2. Open Source Advantage
- Security researchers can review and modify code.
3. Powerful Command Line
- The Linux terminal allows automation, scripting, and rapid system control.
4. Most Servers Run Linux
- A large percentage of internet servers operate on Linux, making it essential for security professionals.
5. Cybersecurity Tools are Built for Linux
Many penetration testing tools run natively on Linux.
3. Linux Distributions Used in Security
A Linux distribution (distro) is a complete operating system built on the Linux kernel with additional tools and software.
Different distributions are designed for different purposes.
Kali Linux

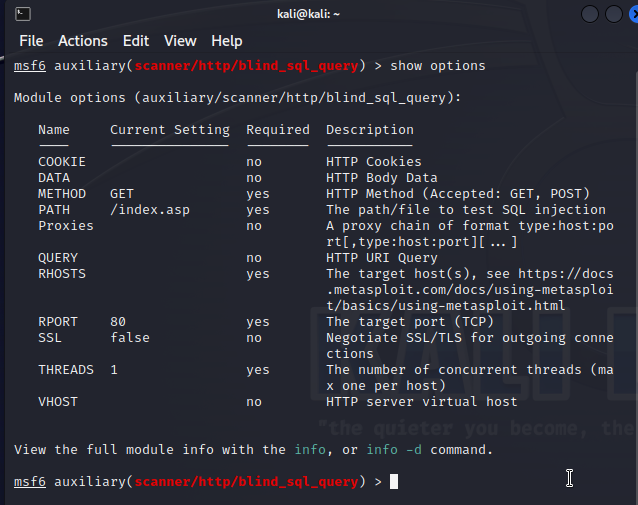
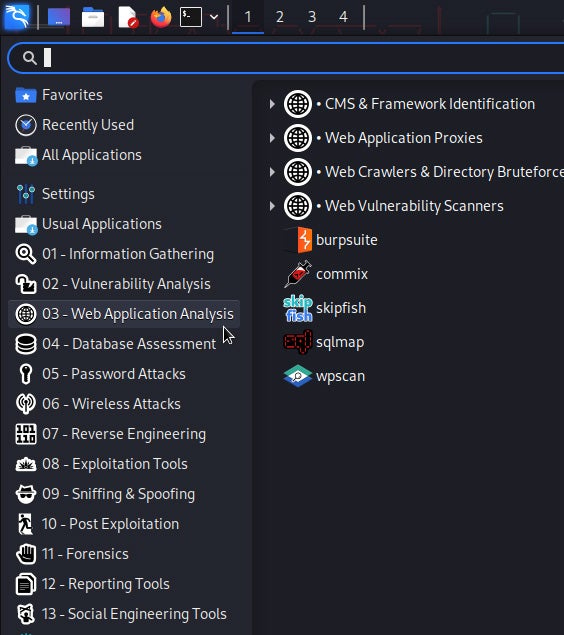

Kali Linux is one of the most popular operating systems for penetration testing and ethical hacking.
Features include:
- Pre-installed penetration testing tools
- Network scanning utilities
- Wireless attack tools
- Digital forensics capabilities
It is widely used by:
- Ethical hackers
- Penetration testers
- Cybersecurity researchers
Parrot Security OS
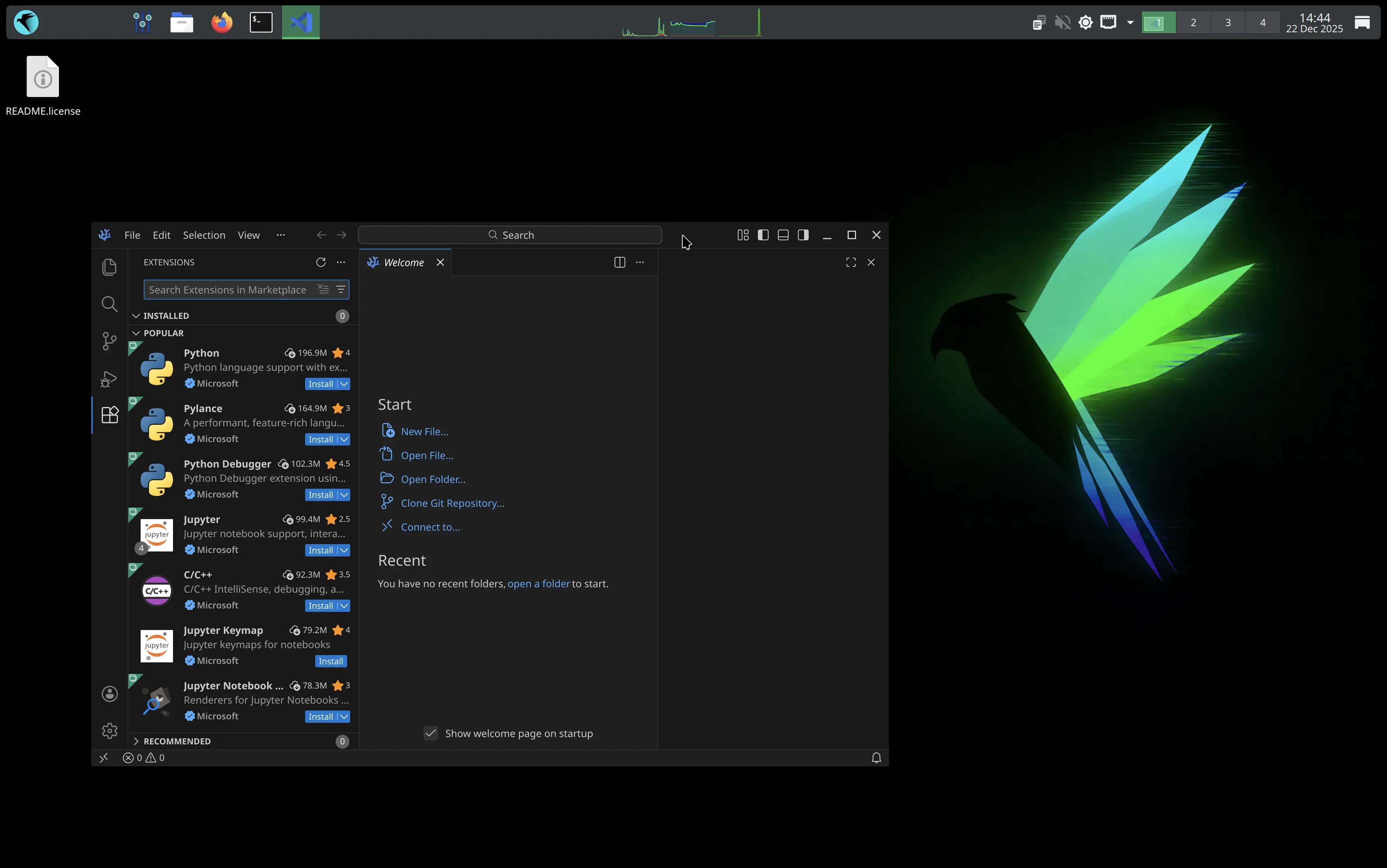

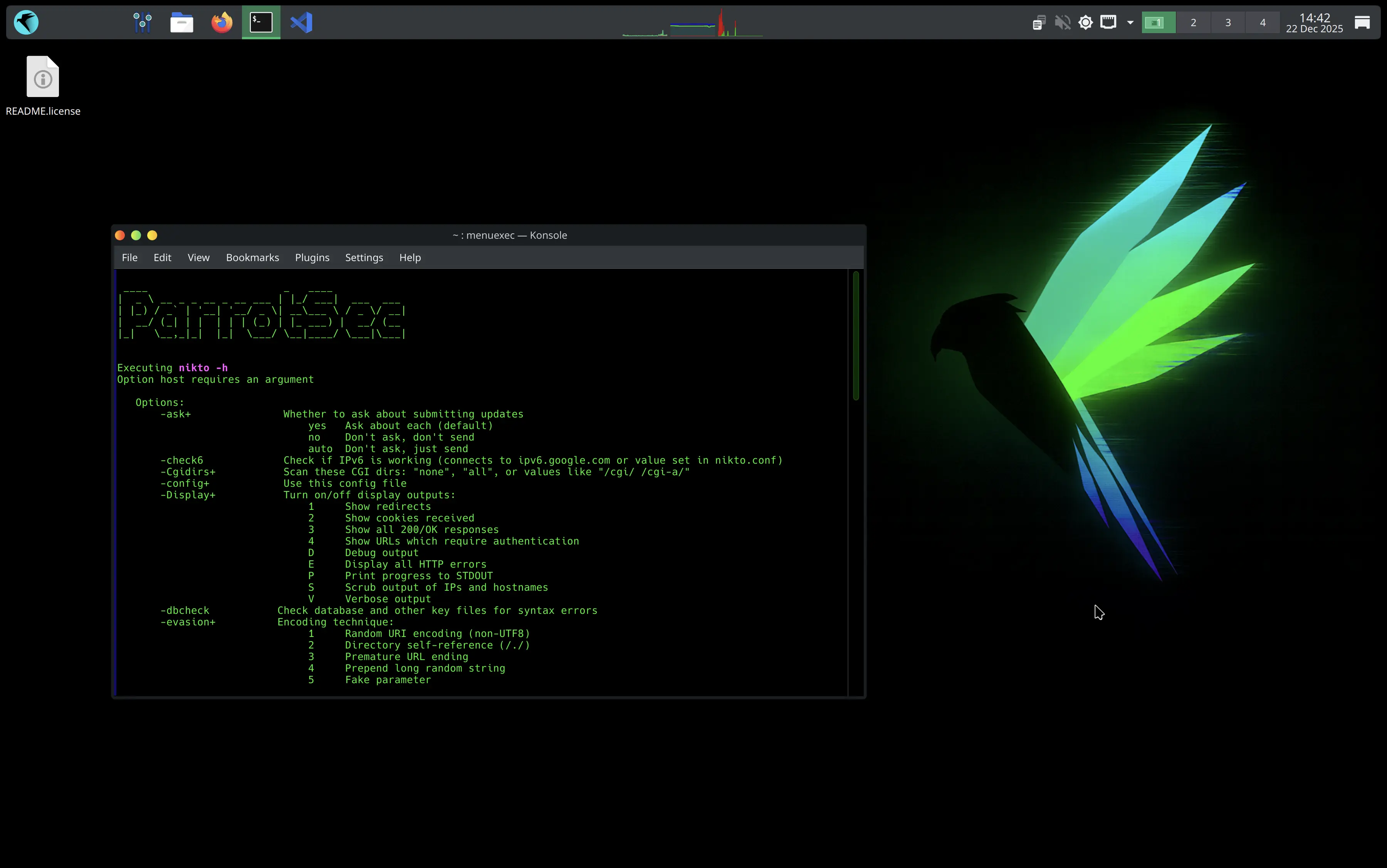
Parrot Security OS is another Linux distribution focused on security, privacy, and digital forensics.
Key features:
- Lightweight and fast
- Built-in anonymity tools
- Secure development environment
- Penetration testing toolkit
Ubuntu

Ubuntu is one of the most beginner-friendly Linux distributions.
It is commonly used for:
- Linux learning
- Server management
- Cloud computing
- Security labs
Ubuntu is often recommended for beginners before moving into advanced security distributions.
4. Ethical Hacking and Security Roles that Require Linux
Many cybersecurity professionals rely heavily on Linux in their daily work.
Common Cybersecurity Roles Using Linux
1. Penetration Tester
- Simulates cyber attacks to find vulnerabilities.
2. Ethical Hacker
- Identifies weaknesses in systems legally and responsibly.
3. Security Analyst
- Monitors networks and investigates threats.
4. Digital Forensics Investigator
- Analyzes compromised systems and evidence.
5. SOC Analyst (Security Operations Center)
- Monitors real-time security alerts.
Most tools used in these roles are designed for Linux environments.
5. Installing Linux (Virtual Machine and Dual Boot)
Before learning cybersecurity tools, students need to install Linux.
Virtual Machine Installation
A virtual machine (VM) allows Linux to run inside another operating system.
Popular VM software includes:
- Oracle VM VirtualBox
- VMware Workstation
Advantages:
- Safe environment for practice
- Easy to install and remove
- No risk to the main system
Dual Boot Installation
Dual boot allows users to install two operating systems on the same computer.
Example:
- Windows
- Linux
When the computer starts, the user can choose which OS to load.
Advantages:
- Full hardware performance
- Better for advanced users
6. Basic Linux System Architecture
Linux is made up of several important components.
1. Kernel
The kernel is the core of the operating system.
It manages:
- CPU
- Memory
- Devices
- Processes
2. Shell
The shell is the interface that allows users to interact with the system.
Common shell:
- Bash (Bourne Again Shell)
The shell interprets commands entered by the user.
3. File System
Linux organizes files in a hierarchical structure.
Important directories include:
| Directory | Purpose |
|---|---|
/home |
User files |
/etc |
System configuration |
/var |
Logs and variable data |
/bin |
Essential system commands |
/root |
Root user directory |
4. Applications
Applications are programs installed on Linux such as:
- Web browsers
- Security tools
- Network analyzers
- Programming software
Summary
In this module, students learned:
- What Linux is
- Why Linux is essential for cybersecurity
- Popular Linux distributions used in security
- Cybersecurity careers that require Linux
- How Linux can be installed
- Basic architecture of the Linux operating system
This knowledge forms the foundation for learning Linux commands and cybersecurity tools.