BUSINESS ANALYSIS. DIGITAL MARKETING. PROJECT MANAGEMENT. ITIL 4 AND MORE
Red Team Ethical Hacking – Course Outline
A comprehensive program designed to equip learners with offensive security skills used to simulate real-world cyberattacks in order to strengthen organizational defenses.
Course Overview
This course provides practical training in adversarial tactics, techniques, and procedures (TTPs) used by professional Red Teams. Learners will understand how attackers think, plan, and execute campaigns — ethically and legally — to test and improve security posture.
Target Audience:
- Cybersecurity professionals
- Penetration testers
- SOC analysts transitioning to offensive roles
- IT professionals (this could complement your Blue Team outline nicely 👀)
Prerequisites:
- Networking fundamentals (TCP/IP, DNS, HTTP)
- Basic Linux & Windows knowledge
- Familiarity with cybersecurity concepts
Module 1: Introduction to Red Teaming



Topics Covered:
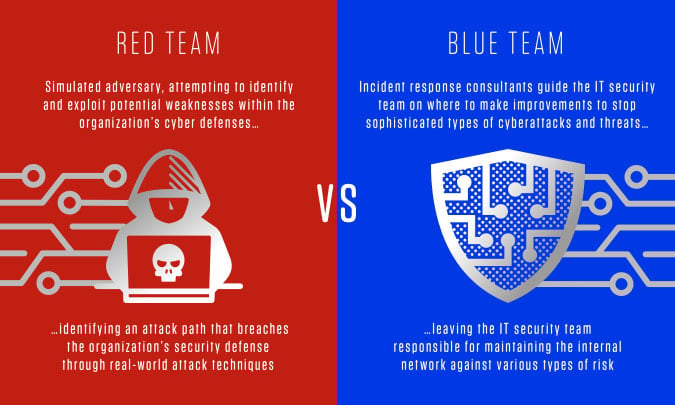
- Red Team vs Blue Team vs Purple Team
- Ethical hacking legal frameworks & rules of engagement
- Red Team methodologies (MITRE ATT&CK overview)
- Scope definition and engagement planning
Learning Outcomes:
- Understand Red Team objectives and responsibilities
- Explain offensive security methodologies
- Identify legal and ethical considerations
Module 2: Reconnaissance & Intelligence Gathering
Topics Covered:
- Open Source Intelligence (OSINT)
- Passive vs Active Reconnaissance
- Social media intelligence
- Network footprinting and scanning
Tools Covered:
- Maltego
- Shodan
- Nmap
- Recon-ng
Learning Outcomes:
- Perform structured intelligence gathering
- Identify attack surfaces
- Map organizational digital footprint
Module 3: Threat Modeling & Attack Planning
Topics Covered:
- Identifying high-value assets
- Mapping attack paths
- Adversary simulation planning
- Developing attack scenarios
Learning Outcomes:
- Create realistic adversary profiles
- Design attack chains
- Plan stealth operations
Module 4: Initial Access Techniques



Topics Covered:
- Phishing and spear phishing simulations
- Exploit development basics
- Credential harvesting
- Wireless attacks
- Physical security testing (authorized scenarios)
Tools Covered:
- Metasploit
- SET (Social-Engineer Toolkit)
- Burp Suite
Learning Outcomes:
- Execute controlled phishing campaigns
- Simulate real-world initial compromise
- Understand exploit frameworks
Module 5: Privilege Escalation & Persistence
Topics Covered:
- Windows & Linux privilege escalation
- Credential dumping
- Token manipulation
- Maintaining access (backdoors, persistence mechanisms)
Tools Covered:
- Mimikatz
- PowerShell Empire
- BloodHound
Learning Outcomes:
- Identify privilege escalation vectors
- Maintain controlled access ethically
- Understand persistence techniques
Module 6: Lateral Movement & Internal Recon
Topics Covered:
- Pivoting techniques
- Pass-the-Hash attacks
- Internal network mapping
- Active Directory attacks
Learning Outcomes:
- Simulate internal compromise
- Exploit weak internal trust relationships
- Navigate segmented networks
Module 7: Command & Control (C2) Infrastructure
Topics Covered:
- C2 frameworks and architecture
- Traffic obfuscation
- Domain fronting concepts
- Evading detection (defensive awareness)
Tools Covered:
- Cobalt Strike
- Sliver
- Covenant
Learning Outcomes:
- Understand C2 operations
- Simulate stealth communication channels
- Identify defensive detection gaps
Module 8: Social Engineering & Human Exploitation
Topics Covered:
- Psychological manipulation techniques
- Pretexting & impersonation
- Phone-based attacks (vishing)
- Awareness testing
Learning Outcomes:
- Design ethical social engineering tests
- Understand human attack vectors
- Measure organizational awareness
Module 9: Post-Exploitation & Data Exfiltration
Topics Covered:
- Sensitive data identification
- Exfiltration techniques (simulated environments only)
- Covering tracks & log evasion concepts
- Operational security (OPSEC)
Learning Outcomes:
- Demonstrate controlled data extraction simulations
- Analyze impact severity
- Maintain engagement safety
Module 10: Reporting & Remediation Guidance
Topics Covered:
- Writing executive summaries
- Technical report documentation
- Risk scoring frameworks
- Debriefing stakeholders
Learning Outcomes:
- Produce professional Red Team reports
- Translate technical findings into business risks
- Recommend mitigation strategies
Activities:
- Full-scope simulated attack
- Real-time adversary emulation
- Blue Team interaction (optional)
- Final reporting and defense presentation
Assessment:
- Practical simulation performance
- Written technical report
- Oral defense presentation
Certification & Assessment
- Practical lab-based evaluation
- Scenario-based penetration simulation
- Final written examination
- Certification of completion
Instructor
CRMNuggets is your go-to platform for insights on Customer Relationship Management (CRM), project management, digital marketing, IT strategies, and business growth tips. Our goal is to help businesses enhance customer experience, optimize processes, and stay ahead with proven strategies and practical guides.
