7 Types Of Security Data In Cybersecurity
Alert data consists of messages generated by intrusion prevention systems (IPSs) or intrusion detection systems…
End Device Logs In Cybersecurity: The Various Types
As previously discussed, host-based intrusion detection systems (HIDS) run on individual hosts. HIDS not only…
Network Logs In Cybersecurity: Facts To Note
Network Logs In Cybersecurity: Facts To Note The tcpdump command-line tool is a very…
Use Of Security Onion As A Source Of Alerts
Use Of Security Onion As A Source Of Alerts Security Onion is an open-source…
The Need For Alert Evaluation In Cybersecurity
The Need For Alert Evaluation In Cybersecurity The threat landscape is constantly changing as…
Elastic Data Core Components In Cybersecurity
A typical network has a multitude of different logs to keep track of and…
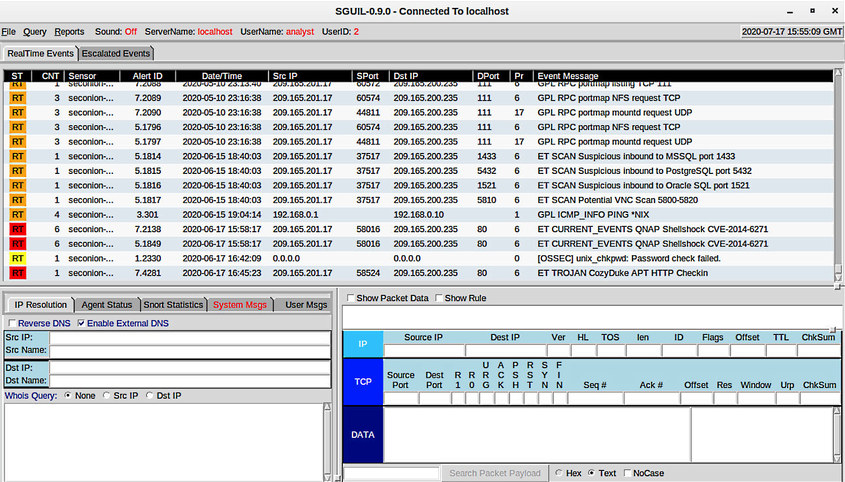
Ways Using Sguil In Investigating Network Data
The primary duty of a cybersecurity analyst is the verification of security alerts. Depending…
Digital Forensics In Cybersecurity: Facts To Note
Digital Forensics In Cybersecurity: Facts To Note Now that you have investigated and identified…
Cyber Killer Chain In Cybersecurity: Facts To Know
The Cyber Killer Chain was developed by Lockheed Martin to identify and prevent cyber…
Understanding Diamond Model Of Intrusion Analysis
Understanding Diamond Model Of Intrusion Analysis The Diamond Model of Intrusion Analysis is made…