
The term Trojan horse originated from Greek mythology. Greek warriors offered the people of Troy (the Trojans) a giant hollow horse as a gift. The Trojans brought the giant horse into their walled city, unaware that it contained many Greek warriors.
At night, after most Trojans were asleep, the warriors burst out of the horse, opened the city gates, and allowed a sizeable force to enter and take over the city.
Trojan horse malware is software that appears to be legitimate, but it contains malicious code which exploits the privileges of the user that runs it. Often, Trojans are found attached to online games.
Users are commonly tricked into loading and executing the Trojan horse on their systems. While playing the game, the user will not notice a problem. In the background, the Trojan horse has been installed on the user’s system. The malicious code from the Trojan horse continues operating even after the game has been closed.
The Trojan horse concept is flexible. It can cause immediate damage, provide remote access to the system, or access through a back door. It can also perform actions as instructed remotely, such as “send me the password file once per week.” This tendency of malware to send data back to the cybercriminal highlights the need to monitor outbound traffic for attack indicators.
Custom-written Trojan horses, such as those with a specific target, are difficult to detect.
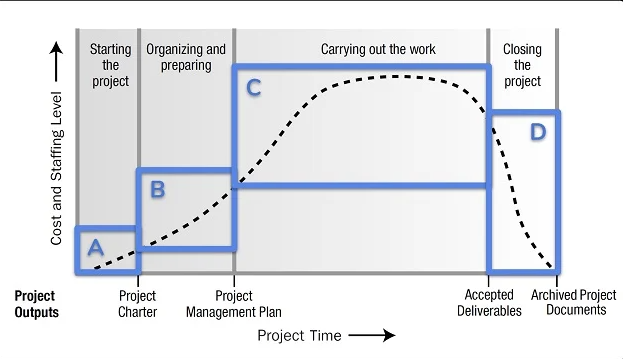
Trojan Horse Classification
Trojan horses are usually classified according to the damage that they cause, or the manner in which they breach a system, as shown in the figure.
| Type of Trojan Horse | Description |
|---|---|
| Remote-access | Enables unauthorized remote access. |
| Data-sending | Provides the threat actor with sensitive data, such as passwords. |
| Destructive | Corrupts or deletes files. |
| Proxy | Uses the victim’s computer as the source device to launch attacks and perform other illegal activities. |
| FTP | Enables unauthorized file transfer services on end devices. |
| Security software disabler | Stops antivirus programs or firewalls from functioning. |
| Denial of Service (DoS) | Slows or halts network activity. |
| Keylogger | Actively attempts to steal confidential information, such as credit card numbers, by recording keystrokes entered into a web form. |
![]()







Leave a Reply