The following points summarize some of the reasons why malware remains a major challenge:
- According to research from Cybersecurity Ventures, by 2021 a new organization will fall victim to a ransomware attack every 11 seconds.
- Ransomware attacks will cost the global economy $6 trillion annually by 2021.
- In 2018, 8 million attempts to steal system resources using cryptojacking malware were observed.
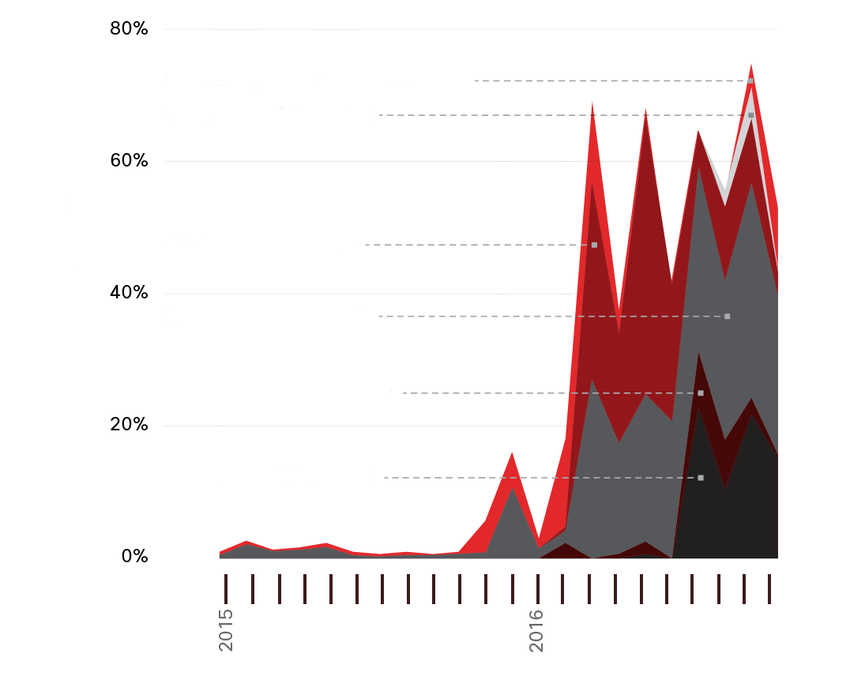
- From 2016 to early 2017, global spam volume increased dramatically. 8 to 10 percent of this spam can be considered to be malicious, as shown in the figure.
- In 2020, it is projected that the average number of cyber attacks per macOS device will rise from 4.8 in 2018 to 14.2 in 2020.
- Several common types of malware have been found to significantly change features in less than 24 hours in order to evade detection.
Endpoint Security
News media commonly cover external network attacks on enterprise networks. These are some examples of such attacks:
- DoS attacks on an organization’s network to degrade or even halt public access to it
- Breach of an organization’s webserver to deface their web presence
- Breach of an organization’s data servers and hosts to steal confidential information
Various network security devices are required to protect the network perimeter from outside access. As shown in the figure, these devices could include a hardened router that is providing VPN services, a next-generation firewall (ASA, in the figure), an IPS appliance, and an authentication, authorization, and accounting (AAA) services server (AAA Server, in the figure).
Specifically, there are two internal LAN elements to secure:
- Endpoints – Hosts commonly consist of laptops, desktops, printers, servers, and IP phones, all of which are susceptible to malware-related attacks.
- Network infrastructure – LAN infrastructure devices interconnect endpoints and typically include switches, wireless devices, and IP telephony devices. Most of these devices are susceptible to LAN-related attacks including MAC address table overflow attacks, spoofing attacks, DHCP related attacks, LAN storm attacks, STP manipulation attacks, and VLAN attacks.
Host-Based Malware Protection
This is software that is installed on a host to detect and mitigate viruses and malware. Examples are Windows Defender Virus & Threat Protection, Cisco AMP for Endpoints, Norton Security, McAfee, Trend Micro, and others. Antimalware programs may detect viruses using three different approaches:
- Signature-based – This approach recognizes various characteristics of known malware files.
- Heuristics-based – This approach recognizes general features shared by various types of malware.
- Behaviour-based – This approach employs analysis of suspicious behaviour.
Many antivirus programs are able to provide real-time protection by analyzing data as it is used by the endpoint. These programs also scan for existing malware that may have entered the system prior to it being recognizable in real-time.
Agent-based antivirus running in each virtualized system can be a serious drain on system resources. Agentless antivirus for virtual hosts involves the use of a special security virtual appliance that performs optimized scanning tasks on the virtual hosts. An example of this is VMware’s vShield.
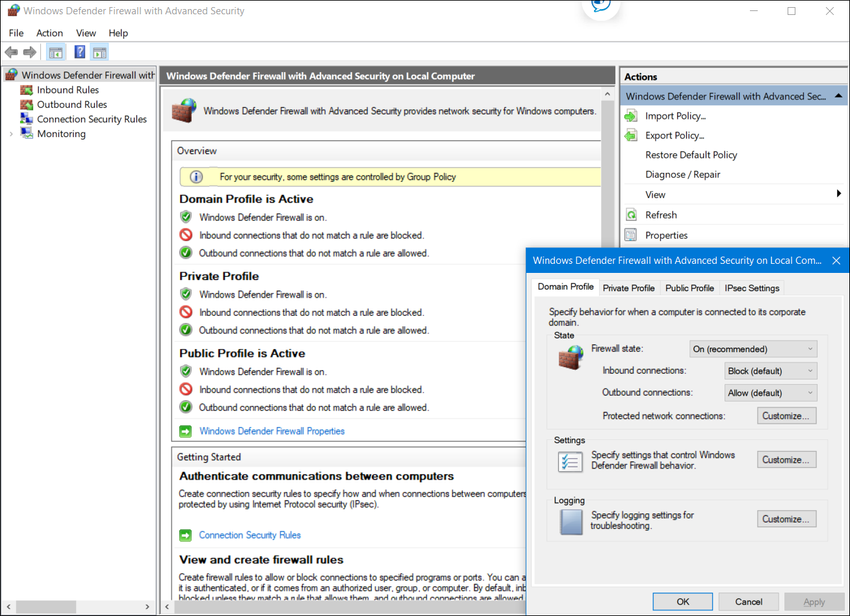
This software is installed on a host. It restricts incoming and outgoing connections to connections initiated by that host only. Some firewall software can also prevent a host from becoming infected and stop infected hosts from spreading malware to other hosts. This function is included in some operating systems. For example, Windows includes Windows Defender Firewall with Advanced Security as shown in the figure.
It is recommended to install a host-based suite of security products on home networks as well as business networks. These host-based security suites include antivirus, anti-phishing, safe browsing, a Host-based intrusion prevention system, and firewall capabilities. These various security measures provide a layered defence that will protect against the most common threats.
Search the internet for the AVTest organization to learn more about AV-TEST.
Network-Based Malware Protection
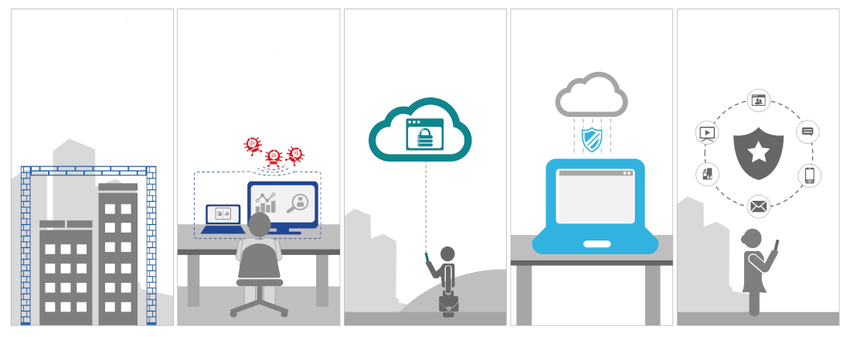
Protecting endpoints in a borderless network can be accomplished using network-based, as well as host-based techniques, as shown in the figure above. The following are examples of devices and techniques that implement host protections at the network level.
- Advanced Malware Protection (AMP) – This provides endpoint protection from viruses and malware.
- Email Security Appliance (ESA) – This provides filtering of SPAM and potentially malicious emails before they reach the endpoint. An example is the Cisco ESA.
- Web Security Appliance (WSA) – This provides filtering of websites and blacklisting to prevent hosts from reaching dangerous locations on the web. The Cisco WSA provides control over how users access the internet and can enforce acceptable use policies, control access to specific sites and services, and scan for malware.
- Network Admission Control (NAC) – This permits only authorized and compliant systems to connect to the network.
Action Point
PS: If you would like to have an online course on any of the courses that you found on this blog, I will be glad to do that on an individual and corporate level, I will be very glad to do that I have trained several individuals and groups and they are doing well in their various fields of endeavour. Some of those that I have trained includes staffs of Dangote Refinery, FCMB, Zenith Bank, New Horizons Nigeria among others. Please come on Whatsapp and let’s talk about your training. You can reach me on Whatsapp HERE. Please note that I will be using Microsoft Team to facilitate the training.
I know you might agree with some of the points that I have raised in this article. You might not agree with some of the issues raised. Let me know your views about the topic discussed. We will appreciate it if you can drop your comment. Thanks in anticipation.
Fact Check Policy
CRMNaija is committed to fact-checking in a fair, transparent and non-partisan manner. Therefore, if you’ve found an error in any of our reports, be it factual, editorial, or an outdated post, please contact us to tell us about it.
|
![]()