
An Access Control List in networking is a series of commands that control whether a device forwards or drops packets based on information found in the packet header. When configured, ACLs perform the following tasks:
- They limit network traffic to increase network performance. For example, if a corporate policy does not allow video traffic on the network, ACLs that block video traffic could be configured and applied. This would greatly reduce the network load and increase network performance.
- They provide traffic flow control. ACLs can restrict the delivery of routing updates to ensure that the updates are from a known source.
- They provide a basic level of security for network access. ACLs can allow one host to access a part of the network and prevent another host from accessing the same area. For example, access to the Human Resources network can be restricted to authorized users.
- They filter traffic based on traffic type. For example, an ACL can permit email traffic but block all Telnet traffic.
- The screen hosts permit or deny access to network services. ACLs can permit or deny a user to access file types, such as FTP or HTTP.
In addition to either permitting or denying traffic, ACLs can be used for selecting types of traffic to be analyzed, forwarded, or processed in other ways. For example, ACLs can be used to classify traffic to enable priority processing. This capability is similar to having a VIP pass at a concert or sporting event.
The VIP pass gives selected guests privileges not offered to general admission ticket holders, such as priority entry or being able to enter a restricted area.
What Is an ACL?
ACLs: Important Features
Extended ACLs filter IPv4 packets based on several attributes that include:
- Protocol type
- Source IPv4 address
- Destination IPv4 address
- Source TCP or UDP ports
- Destination TCP or UDP ports
- Optional protocol type information for finer control
Standard and extended ACLs can be created using either a number or a name to identify the ACL and its list of statements.
Using numbered ACLs is an effective method for determining the ACL type on smaller networks with more homogeneously defined traffic. However, a number does not provide information about the purpose of the ACL. For this reason, a name can be used to identify a Cisco ACL.
By configuring ACL logging, an ACL message can be generated and logged when traffic meets the permit or deny criteria defined in the ACL.
Cisco ACLs can also be configured to only allow TCP traffic that has an ACK or RST bit set, so that only traffic from an established TCP session is permitted. This can be used to deny any TCP traffic from outside the network that is trying to establish a new TCP session.
SNMP
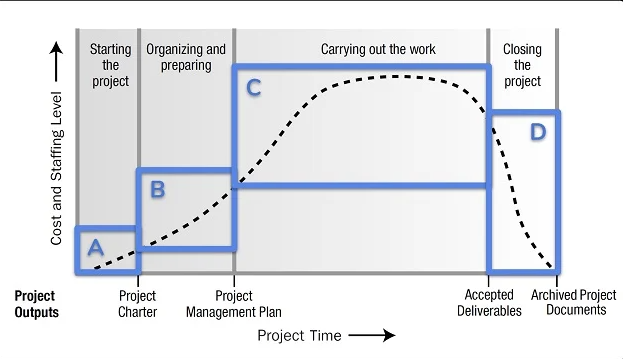
As shown in the figure, the SNMP system consists of two elements.
- SNMP manager that runs SNMP management software.
- SNMP agents are the nodes being monitored and managed.
The Management Information Base (MIB) is a database on the agents that stores data and operational statistics about the device.
To configure SNMP on a networking device, it is first necessary to define the relationship between the manager and the agent.
The SNMP manager is part of a network management system (NMS). The SNMP manager runs SNMP management software.
As shown in the figure, the SNMP manager can collect information from an SNMP agent by using the “get” action and can change configurations on an agent by using the “set” action. In addition, SNMP agents can forward the information directly to a network manager by using “traps”.
NetFlow
NetFlow in the Network
NetFlow technology has seen several generations that provide more sophistication in defining traffic flows, but “original NetFlow” distinguished flows using a combination of seven fields. Should one of these fields vary in value from another packet, the packets could be safely determined to be from different flows:
- Source IP address
- Destination IP address
- Source port number
- Destination port number
- Layer 3 protocol type
- Type of Service (ToS) marking
- Input logical interface
The first four of the fields NetFlow uses to identify a flow should be familiar. The source and destination IP addresses, plus the source and destination ports, identify the connection between the source and destination application.
The Layer 3 protocol type identifies the type of header that follows the IP header (usually TCP or UDP, but other options include ICMP). The ToS byte in the IPv4 header holds information about how devices should apply quality of service (QoS) rules to the packets in that flow.
Port Mirroring
Traffic Sniffing Using a Switch
Syslog Servers
When certain events occur on a network, networking devices have trusted mechanisms to notify the administrator with detailed system messages.
These messages can be either non-critical or significant. Network administrators have a variety of options for storing, interpreting, and displaying these messages, and for being alerted to those messages that could have the greatest impact on the network infrastructure.
The most common method of accessing system messages is to use a protocol called Syslog.
Many networking devices support Syslog, including routers, switches, application servers, firewalls, and other network appliances. The Syslog protocol allows networking devices to send their system messages across the network to Syslog servers.
Syslog
The Syslog logging service provides three primary functions:
- The ability to gather logging information for monitoring and troubleshooting
- The ability to select the type of logging information that is captured
- The ability to specify the destination of captured Syslog messages
NTP
Typically, the date and time settings on a network device can be set using one of two methods:
- Manual configuration of the date and time
- Configuring the Network Time Protocol (NTP)
As a network grows, it becomes difficult to ensure that all infrastructure devices are operating with synchronized time. Even in a smaller network environment, the manual method is not ideal. If a device reboots, how will it get an accurate date and timestamp?
A better solution is to configure the NTP on the network. This protocol allows routers on the network to synchronize their time settings with an NTP server. A group of NTP clients that obtain time and date information from a single source have more consistent time settings.
When NTP is implemented in the network, it can be set up to synchronize to a private master clock or it can synchronize to a publicly available NTP server on the Internet.
NTP networks use a hierarchical system of time sources.
Each level in this hierarchical system is called a stratum. The stratum level is defined as the number of hop counts from the authoritative source. The synchronized time is distributed across the network using NTP. The figure displays a sample NTP network.
NTP Stratum Levels
NTP servers are arranged in three levels known as strata:
- Stratum 0 – An NTP network gets the time from authoritative time sources. These authoritative time sources, also referred to as stratum 0 devices, are high-precision timekeeping devices assumed to be accurate and with little or no delay associated with them.
- Stratum 1 – The stratum 1 devices are directly connected to the authoritative time sources. They act as the primary network time standard.
- Stratum 2 and lower strata – The stratum 2 servers are connected to stratum 1 devices through network connections. Stratum 2 devices, such as NTP clients, synchronize their time using the NTP packets from stratum 1 servers. They could also act as servers for stratum 3 devices.
Smaller stratum numbers indicate that the server is closer to the authorized time source than larger stratum numbers. The larger the stratum number, the lower the stratum level.
The max hop count is 15. Stratum 16, the lowest stratum level, indicates that a device is unsynchronized. Time servers on the same stratum level can be configured to act as a peer with other time servers on the same stratum level for backup or verification of time.
AAA Servers
| AAA Provides | Description |
|---|---|
| Authentication |
|
| Authorization |
|
| Accounting |
|
| TACACS+ | RADIUS | |
|---|---|---|
| Functionality | Separates AAA according to the AAA architecture, allowing modularity of the security server implementation | Combines authentication and authorization but separates accounting, allowing less flexibility in implementation than TACACS+ |
| Standard | Mostly Cisco supported | Open/RFC standard |
| Transport | TCP | UDP |
| Protocol CHAP | Bidirectional challenge and response as used in Challenge Handshake Authentication Protocol (CHAP) | Unidirectional challenge and response from the RADIUS security server to the RADIUS client |
| Confidentiality | Entire packet encrypted | Password encrypted |
| Customization | Provides authorization of router commands on a per-user or per-group basis | Has no option to authorize router commands on a per-user or per-group basis |
| Accounting | Limited | Extensive |
Virtual Private Network
The logical connections can be made at either Layer 2 or Layer 3. Common examples of Layer 3 VPNs are GRE, Multiprotocol Label Switching (MPLS), and IPsec. Layer 3 VPNs can be point-to-point site connections, such as GRE and IPsec, or they can establish any-to-any connectivity to many sites using MPLS.
IPsec is a suite of protocols developed with the backing of the IETF to achieve secure services over IP packet-switched networks.
Action Point
PS: If you would like to have an online course on any of the courses that you found on this blog, I will be glad to do that on an individual and corporate level, I will be very glad to do that because I have trained several individuals and groups and they are doing well in their various fields of endeavour. Some of those that I have trained include the staff of Dangote Refinery, FCMB, Zenith Bank, and New Horizons Nigeria among others. Please come on Whatsapp and let’s talk about your training. You can reach me on Whatsapp HERE. Please note that I will be using Microsoft Team to facilitate the training.
I know you might agree with some of the points that I have raised in this article. You might not agree with some of the issues raised. Let me know your views about the topic discussed. We will appreciate it if you can drop your comment. Thanks in anticipation.
Fact Check Policy
CRMNIGERIA is committed to fact-checking in a fair, transparent and non-partisan manner. Therefore, if you’ve found an error in any of our reports, be it factual, editorial, or an outdated post, please contact us to tell us about it.
|
![]()







Leave a Reply