
For example, consider two people communicating face-to-face. Prior to communicating, they must agree on how to communicate. If the communication is using voice, they must first agree on the language. Next, when they have a message to share, they must be able to format that message in a way that is understandable. For example, if someone uses the English language, but has poor sentence structure, the message can easily be misunderstood.
Similarly, network protocols specify many features of network communication, as shown in the figure.
Network Protocols
Note: IP in this course refers to both the IPv4 and IPv6 protocols. IPv6 is the most recent version of IP and will eventually replace the more common IPv4.
The TCP/IP Protocol Suite
Message Formatting and Encapsulation
Message Size
Message Timing
Message timing is also very important in network communications. Message timing includes the following:
- Flow Control – This is the process of managing the rate of data transmission. Flow control defines how much information can be sent and the speed at which it can be delivered. For example, if one person speaks too quickly, it may be difficult for the receiver to hear and understand the message. In network communication, there are network protocols used by the source and destination devices to negotiate and manage the flow of information.
- Response Timeout – If a person asks a question and does not hear a response within an acceptable amount of time, the person assumes that no answer is coming and reacts accordingly. The person may repeat the question or instead, may go on with the conversation. Hosts on the network use network protocols that specify how long to wait for responses and what action to take if a response timeout occurs.
- Access method – This determines when someone can send a message. Click Play in the figure to see an animation of two people talking at the same time, then a “collision of information” occurs, and it is necessary for the two to back off and start again. Likewise, when a device wants to transmit on a wireless LAN, it is necessary for the WLAN network interface card (NIC) to determine whether the wireless medium is available.
Unicast, Multicast, and Broadcast
Hosts on a network use similar delivery options to communicate. These methods of communication are called unicast, multicast, and broadcast.
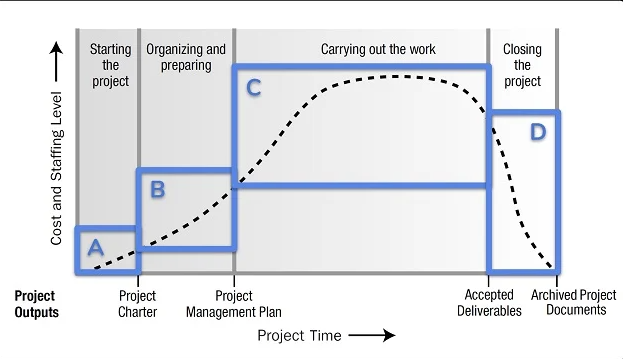
The Benefits of Using a Layered Model
Complex concepts such as how a network operates can be difficult to explain and understand. For this reason, a layered model is used to modularize the operations of a network into manageable layers.
These are the benefits of using a layered model to describe network protocols and operations:
- Assisting in protocol design because protocols that operate at a specific layer have defined information that they act upon and a defined interface to the layers above and below
- Fostering competition because products from different vendors can work together
- Preventing technology or capability changes in one layer from affecting other layers above and below
- Providing a common language to describe networking functions and capabilities
As shown in the figure, there are two-layered models that are used to describe network operations:
- Open System Interconnection (OSI) Reference Model
- TCP/IP Reference Model
The OSI Reference Model
It also describes the interaction of each layer with the layers directly above and below.
| OSI Model Layer | Description |
|---|---|
| 7 – Application | The application layer contains protocols used for process-to-process communications. |
| 6 – Presentation | The presentation layer provides for common representation of the data transferred between application layer services. |
| 5 – Session | The session layer provides services to the presentation layer to organize its dialogue and to manage data exchange. |
| 4 – Transport | The transport layer defines services to segment, transfer, and reassemble the data for individual communications between the end devices. |
| 3 – Network | The network layer provides services to exchange the individual pieces of data over the network between identified end devices. |
| 2 – Data Link | The data link layer protocols describe methods for exchanging data frames between devices over a common media |
| 1 – Physical | The physical layer protocols describe the mechanical, electrical, functional, and procedural means to activate, maintain, and de-activate physical connections for a bit transmission to and from a network device. |
The TCP/IP Protocol Model
| TCP/IP Model Layer | Description |
|---|---|
| 4 – Application | Represents data to the user, plus encoding and dialog control. |
| 3 – Transport | Supports communication between various devices across diverse networks. |
| 2 – Internet | Determines the best path through the network. |
| 1 – Network Access | Controls the hardware devices and media that make up the network. |
Facts About Network Communication Process
Networks of Many Sizes
First and foremost, networks come in all sizes. They range from simple networks that consist of two computers to networks connecting millions of devices. Simple home networks let you share resources, such as printers, documents, pictures, and music, among a few local end devices. In this article, I want to discuss some facts about a network communication process.
Small office and home office (SOHO) networks allow people to work from home or a remote office. Many self-employed workers use these types of networks to advertise and sell products, order supplies and communicate with customers.
Businesses and large organizations use networks to provide consolidation, storage, and access to information on network servers. Networks provide email, instant messaging, and collaboration among employees. Many organizations use their network’s connection to the internet to provide products and services to customers.
The internet is the largest network in existence. In fact, the term internet means a “network of networks”. It is a collection of interconnected private and public networks.
In small businesses and homes, many computers function as both servers and clients on the network. This type of network is called a peer-to-peer network.
Client-Server Communications
Client computers have software installed, such as web browsers, email clients, and file transfers applications. This software enables them to request and display the information obtained from the server. A single computer can also run multiple types of client software. For example, a user can check email and view a web page while listening to the internet radio.
- File Server – The file server stores corporate and user files in a central location.
- Web Server – The web server runs web server software that allows many computers to access web pages.
- Email Server – The email server runs email server software that enables emails to be sent and received.
Typical Sessions
Student
Surgeon
Dr Ismael Awad is an oncologist who performs surgery on cancer patients. He frequently needs to consult with radiologists and other specialists on patient cases. The hospital that Dr Awad works for subscribes to a special service called a cloud. The cloud allows medical data, including patient x-rays and MRIs to be stored in a central location that is accessed over the internet. In this way, the hospital does not need to manage paper patient records and X-ray films.
When a patient has an X-ray taken, the image is digitized as computer data. The X-ray is then prepared by hospital computers to be sent to the medical cloud service. Because security is very important when working with medical data, the hospital uses network services that encrypt the image data and patient information. This encrypted data cannot be intercepted and read as it travels across the internet to the cloud service provider’s data centres. The data is addressed so that it can be routed to the cloud provider’s data centre to reach the correct services that provide storage and retrieval of high-resolution digital images.
Tracing the Path
Action Point
PS: If you would like to have an online course on any of the courses that you found on this blog, I will be glad to do that on an individual and corporate level, I will be very glad to do that because I have trainned several individuals and groups and they are doing well in their various fields of endeavour. Some of those that I have trainned include staff of Dangote Refinery, FCMB, Zenith Bank, and New Horizons Nigeria among others. Please come on Whatsapp and let’s talk about your training. You can reach me on Whatsapp HERE. Please note that I will be using Microsoft Team to facilitate the training.
I know you might agree with some of the points that I have raised in this article. You might not agree with some of the issues raised. Let me know your views about the topic discussed. We will appreciate it if you can drop your comment. Thanks in anticipation.
Fact Check Policy
TECHMANIA is committed to fact-checking in a fair, transparent and non-partisan manner. Therefore, if you’ve found an error in any of our reports, be it factual, editorial, or an outdated post, please contact us to tell us about it.
|
![]()










Leave a Reply