
DNS Resolves Names to IP Addresses
The DNS Domain Hierarchy
The DNS consists of a hierarchy of generic top-level domains (gTLD) which consist of .com, .net, .org, .gov, .edu, and numerous country-level domains, such as .br (Brazil), .es (Spain), .uk (United Kingdom), etc. At the next level of the DNS hierarchy are second-level domains. These are represented by a domain name that is followed by a top-level domain.
Subdomains are found at the next level of the DNS hierarchy and represent some division of the second-level domain. Finally, a fourth level can represent a host in a subdomain.
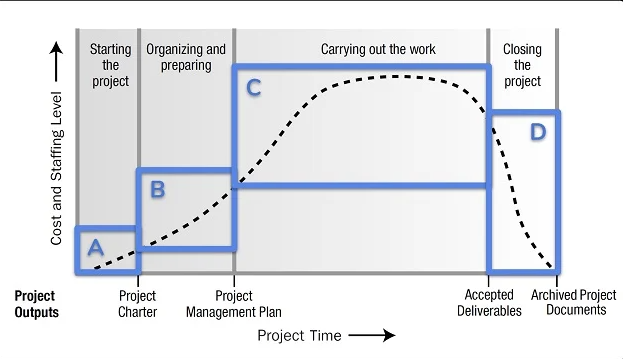
Each element of a domain specification is sometimes called a label. The labels move from the top of the hierarchy downward from right to left. A dot (“.“) at the end of a domain name represents the root server at the top of the hierarchy. The figure illustrates this DNS domain hierarchy.
The different top-level domains represent either the type of organization or the country of origin. Examples of top-level domains are the following:
- .com – a business or industry
- .org – a non-profit organization
- .au – Australia
- .co – Colombia
The DNS Lookup Process
To understand DNS, cybersecurity analysts should be familiar with the following terms:
- Resolver – A DNS client that sends DNS messages to obtain information about the requested domain name space.
- Recursion – The action taken when a DNS server is asked to query on behalf of a DNS resolver.
- Authoritative Server – A DNS server that responds to query messages with information stored in Resource Records (RRs) for a domain name space stored on the server.
- Recursive Resolver – A DNS server that recursively queries for the information asked in the DNS query.
- FQDN – A Fully Qualified Domain Name is the absolute name of a device within the distributed DNS database.
- RR – A Resource Record is a format used in DNS messages that is composed of the following fields: NAME, TYPE, CLASS, TTL, RDLENGTH, and RDATA.
- Zone – A database that contains information about the domain name space stored on an authoritative server.
When attempting to resolve a name to an IP address, a user host, known in the system as a resolver, will first check its local DNS cache. If the mapping is not found there, a query will be issued to the DNS server or servers that are configured in the network addressing properties for the resolver.
These servers may be present at an enterprise or ISP. If the mapping is not found there, the DNS server will query other higher-level DNS servers that are authoritative for the top-level domain in order to find the mapping. These are known as recursive queries.
Because of the potential burden on authoritative top-level domain servers, some DNS servers in the hierarchy maintain caches of all DNS records that they have resolved for a period of time.
These caching DNS servers can resolve recursive queries without forwarding the queries to higher-level servers. If a server requires data for a zone, it will request a transfer of that data from an authoritative server for that zone. The process of transferring blocks of DNS data between servers is known as a zone transfer.
DNS Message Format
The DNS server stores different types of RRs used to resolve names. These records contain the name, address, and type of record. Here is a list of some of these record types:
- A – An end device IPv4 address
- NS – An authoritative name server
- AAAA – An end device IPv6 address (pronounced quad-A)
- MX – A mail exchange record
When a client makes a query, the server’s DNS process first looks at its own records to resolve the name. If it is unable to resolve the name using its stored records, it contacts other servers to resolve the name.
After a match is found and returned to the original requesting server, the server temporarily stores the numbered address in the event that the same name is requested again.
| DNS message section | Description |
|---|---|
| Question | The question for the server. It contains the domain name to be resolved, the class of domain, and the query type. |
| Answer | The DNS resource record, or RR, for the query including the resolved IP address depending on the RR type. |
| Authority | Contains the RRs for the domain authority. |
| Additional | Relevant to query responses only. Consists of RRs that hold additional information that will make query resolution more efficient |
Dynamic DNS
DNS requires registrars to accept and distribute DNS mappings from organizations that wish to register domain names and IP address mappings. After the initial mapping has been created, a process that can take 24 hours or more, changes to the IP address that is mapped to the domain name can be made by contacting the registrar or using an online form to make the change.
However, because of the time it takes for this process to occur and the new mapping to be distributed in the domain name system, the change can take hours before the new mapping is available to resolvers.
In situations in which an ISP is using DHCP to provide addresses to a domain, it is possible that the address that is mapped to the domain could expire and a new address be granted by the ISP. This would result in a disruption of connectivity to the domain through DNS. A new approach was necessary to allow organizations to make fast changes to the IP address that is mapped to a domain.
When a change is detected, the DDNS provider is immediately informed of the change and the mapping between the user’s subdomain and the internet IP address is immediately updated, as shown in the figure. DDNS does not use a true DNS entry for a user’s IP address. Instead, it acts as an intermediary.
The DDNS provider’s domain is registered with the DNS, but the subdomain is mapped to a totally different IP address. The DDNS provider service supplies that IP address to the resolver’s second-level DNS server. That DNS server, either at the organization or ISP, provides the DDNS IP address to the resolver.
Dynamic DNS can be abused by threat actors in various ways. Free DDNS services are especially useful to threat actors. DDNS can be used to facilitate the rapid change of IP address for malware command-and-control servers after the current IP address has become widely blocked. In this way, the malware can be coded with a URL rather than a static IP address.
DDNS can also be used as a way to exfiltrate data from inside a network because DNS traffic is very common and is frequently considered to be benign. DDNS itself is not malignant, however monitoring DNS traffic that is going to known DDNS services, especially free ones, is very useful for the detection of exploits.
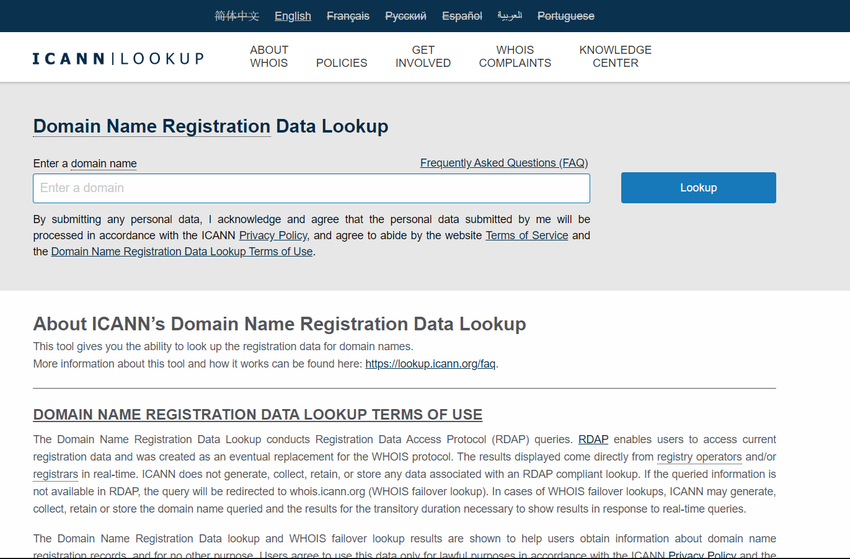
The WHOIS Protocol
Action Point
PS: If you would like to have an online course on any of the courses that you found on this blog, I will be glad to do that on an individual and corporate level, I will be very glad to do that I have trained several individuals and groups and they are doing well in their various fields of endeavour. Some of those that I have trained include staff of Dangote Refinery, FCMB, Zenith Bank, and New Horizons Nigeria among others. Please come on Whatsapp and let’s talk about your training. You can reach me on Whatsapp HERE. Please note that I will be using Microsoft Team to facilitate the training.
I know you might agree with some of the points that I have raised in this article. You might not agree with some of the issues raised. Let me know your views about the topic discussed. We will appreciate it if you can drop your comment. Thanks in anticipation.
Fact Check Policy
TECHMANIA is committed to fact-checking in a fair, transparent and non-partisan manner. Therefore, if you’ve found an error in any of our reports, be it factual, editorial, or an outdated post, please contact us to tell us about it.
|
![]()








Leave a Reply