There are two types of accounts that can be added to a device running Windows 8.1: a Microsoft account and a local account. In this project, you will add both types of accounts to a device. Steps for Completion: 1. On a device running Windows 8.1, hover your mouse to the top-right corner of…
COMPUTER SECURITY
MTA 98-360: Configuring the Start Menu In Windows 8.1
MTA 98-360: Configuring the Start Menu Description: One of the major adjustments from moving to Windows 7 to Windows 8 was the disappearance of the Start button from the desktop. In Windows 8.1, the Start button is back on the desktop but does not display the Start menu. Rather, it displays the Start…
MTA 98-368: Joining a Device to a Network In Windows 8.1
When a device is first configured, it actually belongs to a network called a workgroup. A workgroup is a peer-to-peer network in which devices can communicate and share information with each other. Most home-based users of Windows devices will never even realizethey are on a workgroup. In this article, I will talk about joining…
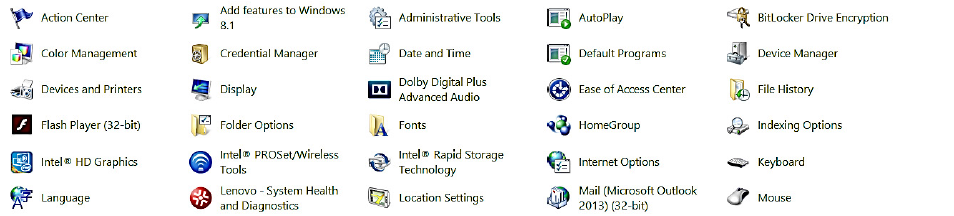
MTA 98-368: Configuring The Control Panel in Windows 8.1
In this exercise, you will review some of the different ways in which you can access the Control Panel. You will also look through the different Control Panel views, and, you will search for an item in the Control Panel. NOTE: Here is a reminder for this and any other exercise involving using…
MTA 98-368: Obtaining A Microsoft Account In Windows 8.1
In order to best utilize features on any Windows device (such as a Surface, Windows Phone, or Xbox), you will need to have a Microsoft account. This account, which used to be known as a Windows Live ID, just needs to be a legitimate email address. A Microsoft account will enable you to: •…
Understanding Common Worm Pattern In Cybersecurity
Types of Malware End devices are especially prone to malware attacks. Therefore, the focus of this topic is on threats to end devices. Malware is short for malicious software or malicious code. It is code or software that is specifically designed to damage, disrupt, steal, or generally inflict some other “bad” or illegitimate action on…
Threat Intelligence Service In Network Security
There is a need for vendors to have a catalogue of known viruses so that they can profile them and share their knowledge with others. The Threat Intelligence Department always take samples of each known viruses, In this article, I willl be talking about Threat Intelligence in Network Security. They look at the…
Understanding SOAR In Network Security
SOAR stands for Security Orchestration, Automation, and Response. The term is used to describe three software capabilities – threat and vulnerability management, security incident response and security operations automation. SOAR allows companies to collect threat-related data from a range of sources and automate responses to low-level threats. What is SOAR SOAR connects all…
Understanding SIEM In Network Security
Understanding SIEM In Network Security Security Information and Event Management was introduced in 2005 It analyses security alerts in real-time. Fundamentally, SIEM does three things. Alert, normalize and store log events. This includes alerts from servers, databases, devices and endpoints. These are stored in a secured central location. SIEM can collect information…
Analysing Secured Email Gateway For Networks
Your email is the very first thing people did when the world when online in the 90s. It comes with very little bandwidth because technology allows for very little bandwidth. It was also so easy and inexpensive to send an email compared to the post office. There are some bulk emails that were sent…
Understanding Sandbox Technology For Networks
Sandbox Technology is a means of isolating applications or data in a virtual environment in order to see how it will behave. It also networks security experts to discover whether an application has malware or not. It studies the behaviour of any application in order to uncover any malicious attack. That means if something unusual…
Some Data Backup Checklists For Users
In many of my previous articles, I have discussed it that you need to make sure that you backup your data. When you do data backup, you are protecting your data from eventual loss. Having a data backup will ensure that you are able to quickly restore your data if anything happens to your data….
6 Common Threats To Wireless Networks
In my previous articles, I have talked about all that you need to know about Home Networks. In this article, I want to look at all that you need to know about Common Threats to Wireless networks. Follow me as we are going to look at that together in this article. Here…
How To Use Windows Easy Transfer
In my previous article, I have talked about some of the facts that you need to know about computer network security generally. In this article, I want to throw more light on how to fo Window Easy Transfer on Windows Operating System. Follow me as we will look at that together in this article. Windows…
10 Types Of Network Security Threats
When it comes to the process of connecting two or more computers together, there are some risks that are associated with it which you have to be aware of. I want to talk about ten different types of such risks in this article. Follow me as we are going to do that together in this…
How To Use Firewall And Anti-Virus For Device Protection
A firewall is a part of the computer system or network that is designed to block unauthorised access from devices. In this article, I want to talk about some of the ways to use firewalls and virus for device protection. Follow me as we are going to look at that together in this article. …
4 Major Types Of Threat Actors In Cyber Attacks
Threat actors include but are not limited to, amateurs, hacktivists, organized crime groups, state-sponsored, and terrorist groups. Threat actors are individuals or groups of individuals who perform cyberattacks. Cyberattacks are intentional malicious acts meant to negatively impact another individual or organization. In this article, I will talk about four types of threat actors in Cyber…
Understanding Network Representation For Networks
Network architects and administrators must be able to show what their networks will look like. They need to be able to easily see which components connect to other components, where they will be located, and how they will be connected. Diagrams of networks often use symbols, like those shown in the figure, to represent the…
Understanding Human-Based Social Engineering
In my previous article, I have talked more about social engineering and some of the reasons why you need to keep your personal data and identity secured. In this article, I want to discuss some of the facts that you need to know about human-based social engineering. Follow me as we are going to look…
Facts About Identity Theft In Computer Security
In my previous articles, I have talked about some of the facts that you need to know about how you can secure yourself online. Please note that the mistake that many people are making is that they always feel that they have nothing that is of importance to a hacker. You should note that…